IPSet (Linux Netfilter/IPTables)
Linux comes equipped with a built-in native firewall which Knocknoc orchestrates via "IPSets". IPSets are a powerful and highly efficient way of making a dynamic firewall on a normal Linux machine. A native feature of the Netfilter code, an IPset is an in-memory list of IPs, that can be referenced in any firewall rules.
Knocknoc can add and remove IPs from an IPset, thereby allowing an arbitrary application of dynamic allow-listing to any Linux box.
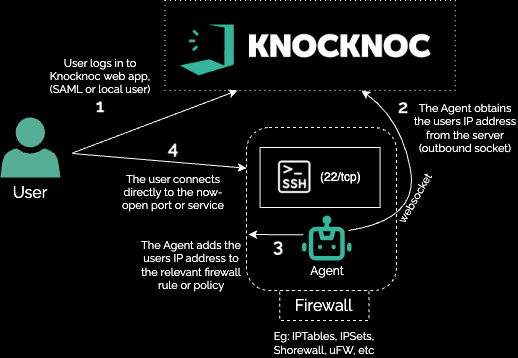
The overall process is:
- Install the Knocknoc agent on the Linux machine requiring access control and enroll it into the Knocknoc server.
- For information how to do so, please consult the Linux Agent Installation documentation
- By default, the Agent will create a number of IPSets for use, including: knoc_ssh, knoc_http, knoc_https. These can be adjusted by editing
/opt/knocknoc-agent/etc/ipset.list- and then restarting withsystemctl restart create-ipsetsnote that IPSet sudo-permissions are now enabled during the Agent installation. If you are migrating from an older version, Knocker can help verify IPSets readiness or update your Agent. - Configure a Knoc in the Knocknoc Server, e.g., allowing certain user-logins to access knoc_http.
- Make use of the IPSets in your firewall. An example for UFW is here, and Shorewall is here. A raw iptables example is at the bottom of this page.
- Remember to block access and default-deny from anyone except those in the Knocknoc authorized list!
Configure the Knoc
Select Knocs and then the Linux / Host firewall
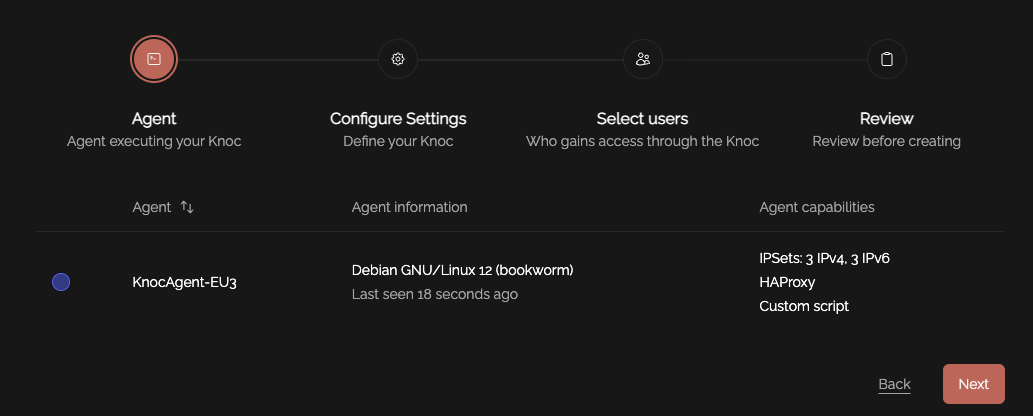
Select the Agent you want to execute the Knoc on:
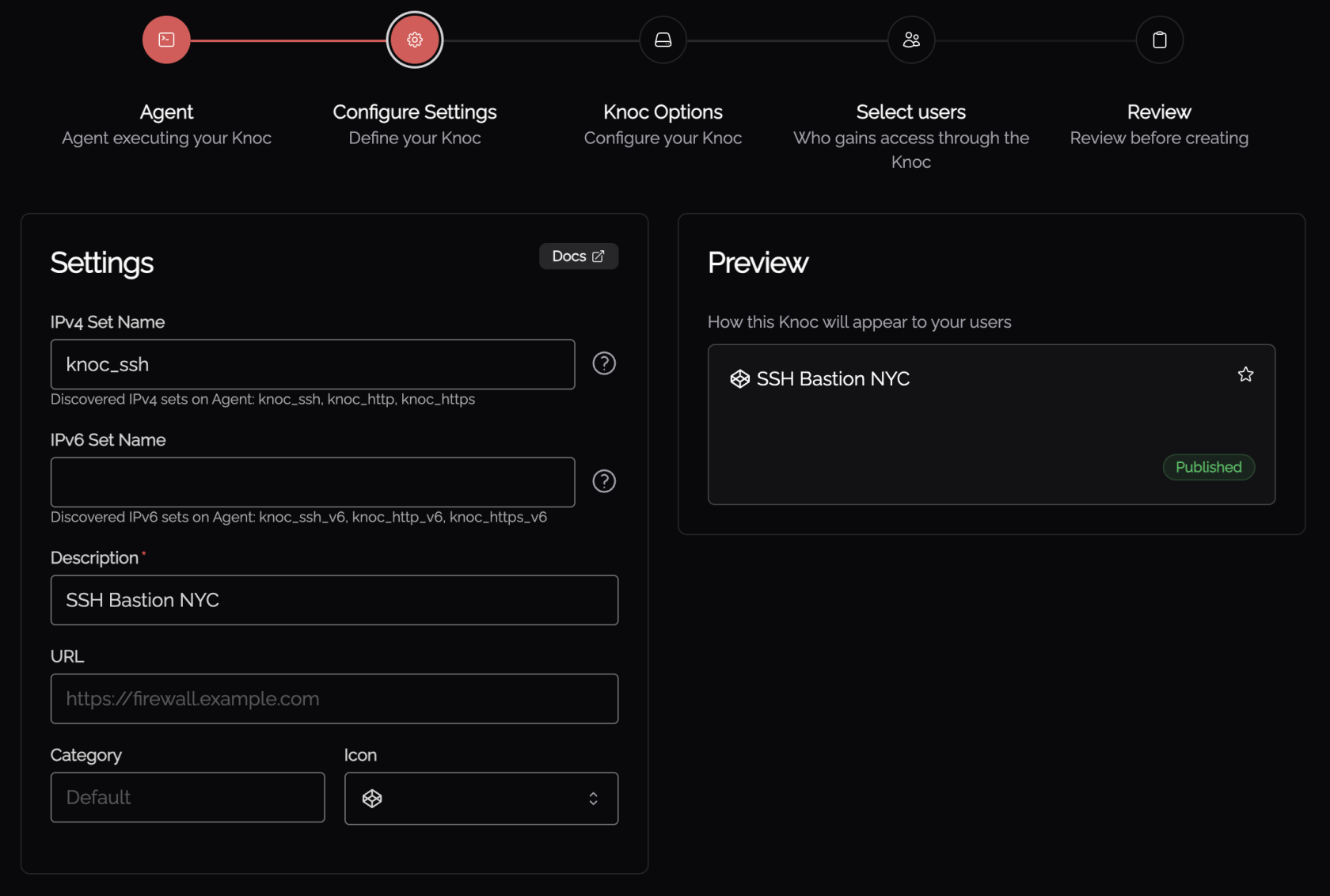
Configure any relevant settings, noting the existing IPSet names are populated. A new IPSet can be defined but must later be created on the relevant Agent server.
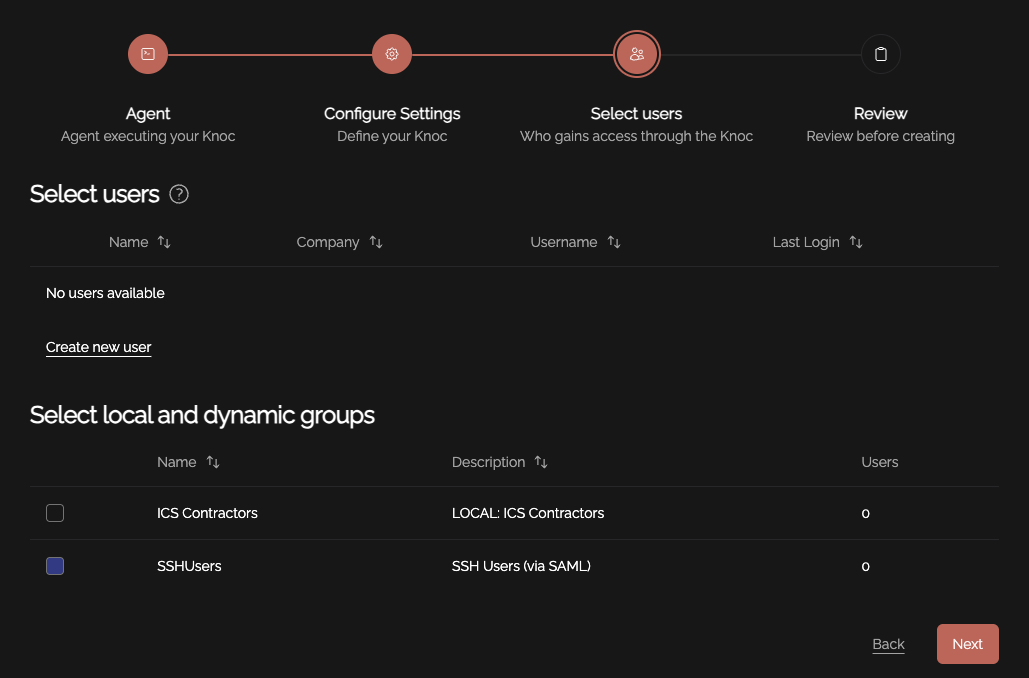
Select the users and/or groups that should be assigned to this Knoc, effectively granting them access on login:
Using the IPSet name in your Firewall
Using the example shown above, anyone successfully logging in to Knocknoc will appear in the "knoc_ssh" IPSet, which then needs to be used by your firewall to allow traffic.
To allowlist IP sources for SSH access, a basic firewall rule needs to be created:
iptables -A INPUT -i eth0 -p tcp --dport 22 -m set --match-set knoc_ssh src -j ACCEPT
You then need to drop packets from other untrusted/unauthenticated sources (if you're not using -P DROP as the default policy), an example would be:
iptables -A INPUT -i eth0 -p tcp --dport 22 -j DROP
Running these two rules on your Linux host is all that's needed to validate the SSH service is protected by Knocknoc.
You're now ready to test
log in as a user to Knocknoc, then attempt to SSH to the machine running the agent which is now protected, given the above firewall rules!
See Shorewall for other examples.
Example deployment - adding MFA to SSH
You can quickly add MFA to SSH by utilizing Knocknoc's built-in TOTP/MFA functionality for local users, or by integrating with your existing IdP. This adds the users IP address to IPTables (via IPSets) as below:
Troubleshooting IPSets
- Confirm the Agent is connecting to the Server - via the Server->Agents page.
- Check the Knoc configuration - what is the IPSet name? (e.g.,
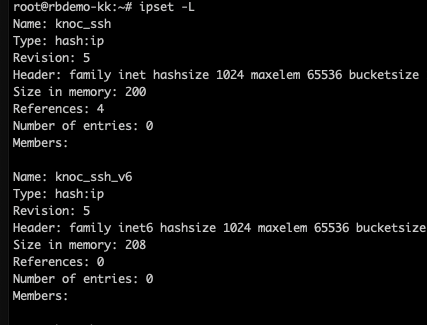
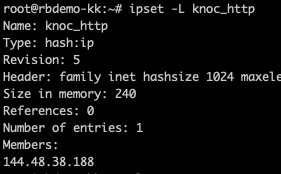
knoc_ssh) - Log in to the machine running the Agent, and use 'ipset' to view any existing entries.
ipset -LThe above shows no "Members", once a user is logged in, it will show their IP address in the relevant IPSet. Note you can also pass the IPSet name: - Check the Agent and/or Server logs, is the Agent receiving the instruction? Is the Knoc linked to the user or group logging in?
- If the IP address is within the IPSet list, the next thing to check is your firewall. Do this with iptables -L -nv as it covers iptables native, shorewall/ufw/etc. Is the IPSet name used correctly?
IPSets not created on boot?
If your IPSets are not loading on boot, you need to check /opt/knocknoc-agent/etc/ipset.list and then restart manually with systemctl restart create-ipsets
List your IPSets to see if they are now loading: ipset -L
Enable the startup script on boot (for systemd/newer Linux hosts): systemctl enable create-ipsets
You can check the status, noting if you do get an error state check the ipset response, as it will error saying the ipsets exist which is a false alarm (see: Set cannot be created: set with the same name already exists):
$ sudo systemctl status create-ipsets
× create-ipsets.service - Create ipset for Knocknoc
Loaded: loaded (/lib/systemd/system/create-ipsets.service; enabled; preset: enabled)
Active: failed (Result: exit-code) since Tue 2025-09-16 23:30:49 UTC; 21h ago
Main PID: 191468 (code=exited, status=1/FAILURE)
CPU: 22ms
Sep 16 23:30:48 demo-kk systemd[1]: Starting create-ipsets.service - Create ipset for Knocknoc...
Sep 16 23:30:49 demo-kk create_ipsets.sh[191487]: ipset v7.17: Set cannot be created: set with the same name already exists
Sep 16 23:30:49 demo-kk create_ipsets.sh[191490]: ipset v7.17: Set cannot be created: set with the same name already existsDoing things manually
If you prefer to manage sudoers, systemd/startup and the IPSet name creation manually, follow the below steps. Alternatively use Knocker to establish these automatically or choose this option as part of the Agent installation.
Sudoers:
Copy the example sudoers file in to place
cp /opt/knocknoc-agent/scripts/sudoers_knocknoc-agent /etc/sudoers.d/
IPSet definitions in the create_ipsets script should be edited to match any ACLs you intend to pass through to the agent for granting/revoking access. An example would be adding "ssh_allowed" which is then entered as the ACL later on.
mv /opt/knocknoc-agent/scripts/create_ipsets.sh /usr/local/sbin/
vi /opt/knocknoc-agent/scripts/create_ipsets.sh
The IPSet must be created on startup or otherwise exist prior to being added/removed from. An example systemd script is packaged with the agent at /opt/knocknoc-agent/scripts/systemd_create-ipset.service, which can be moved to /etc/systemd/system/create-ipset.service and the service started.
vi /opt/knocknoc-agent/scripts/systemd_create-ipset.service
mv /opt/knocknoc-agent/scripts/systemd_create-ipset.service /etc/systemd/system/create-ipset.servicesystemctl start create-ipset
The IPSets can then be listed and verified using: ipset -L
Example custom-script managing IPSets (IPv4 and v6)
Some applications work better if you also add the user to a second blocklist IPset once the access is revoked. This can be used to actively drop established TCP connections where streams or other connections are intentionally actively terminated.
Paste this script into /usr/local/bin/ipset_block.sh, make it executable and update your Knocknoc server backend config to have this path. Note this script assumes you have given the knocknoc-agent sudo rights to run the ipset command.
This script supports IPv4 and IPv6 automatically - note however your IPSet name will automatically have _v4 and _v6 appended as part of the Knocknoc-agent grant process. Therefore the "ACL Name" only needs to be "ssh_allowed" (in these examples) and the script takes care of the rest.
Note that the benefit of the 'blocking' script is that it will effectively terminate any pre-established connections by allowing you to DROP based on the blocked IPSet.
#!/bin/bash
# Wrapper script to allow safe parsing of an ipset command line from sudo
# sudo is run in this script itself, so you need to enable the ipset command in sudoers
# like so:
# make a file in /etc/sudoers.d/knocknoc-agent with this contents:
# knocknoc-agent ALL=(ALL:ALL) NOPASSWD: /usr/sbin/ipset *
set -e -o pipefail
# Define the general_blocked ipset names
general_blocked_v4="knocknoc_blocked"
general_blocked_v6="knocknoc_blocked_v6"
# Validate IPv4 address
function validate_ip() {
local ip=$1
if [[ $ip =~ ^[0-9]{1,3}(\.[0-9]{1,3}){3}$ ]]; then
return 0
else
echo "Invalid IPv4 address"
exit 1
fi
}
# Validate IPv6 address
function validate_ipv6() {
local ip=$1
if getent ahosts "$ip" | grep -q ':'; then
return 0
else
echo "Invalid IPv6 address"
exit 1
fi
}
# Validate setname
function validate_setname() {
local setname=$1
if [[ $setname =~ ^[A-Za-z0-9_]+$ ]]; then
return 0
else
echo "Invalid setname"
exit 1
fi
}
# Validate operation
function validate_op() {
local op=$1
if [[ $op =~ ^(add|del|flush)$ ]]; then
return 0
else
echo "Invalid operation"
exit 1
fi
}
# Validate and assign operation
validate_op "$1"
op="$1"
# Validate and assign setname
validate_setname "$2"
setname="$2"
# Determine if it's an IPv4 or IPv6 address
ip="$3"
if [[ -n "$ip" ]]; then
if [[ $ip =~ ":" ]]; then
validate_ipv6 "$ip"
ip_version="v6"
else
validate_ip "$ip"
ip_version="v4"
fi
fi
# Adjust setname based on IP version
if [[ $ip_version == "v6" ]]; then
setname="${setname}_v6"
general_blocked=$general_blocked_v6
else
general_blocked=$general_blocked_v4
fi
# Execute ipset commands
if [[ "$op" = "flush" ]]; then
# Flush the appropriate set
sudo /usr/sbin/ipset "$op" "$setname"
elif [[ "$op" = "add" ]]; then
# Add IP to the appropriate set
sudo /usr/sbin/ipset "$op" "$setname" "$ip"
# Remove IP from the general blocked set to ensure no conflicts
sudo /usr/sbin/ipset del "$general_blocked" "$ip" || true
elif [[ "$op" = "del" ]]; then
# Remove IP from the appropriate set
sudo /usr/sbin/ipset "$op" "$setname" "$ip"
# Add IP to the general blocked set for tracking purposes
sudo /usr/sbin/ipset add "$general_blocked" "$ip" || true
else
echo "Unknown operation: $op"
exit 1
fiExample IPSet startup/creation script
This needs to run on startup to ensure the IPSets are in place on the host ready for the IP addresses to be added. Note this appends _v4 and _v6 to ensure either IPv4/IPv6 are appropriately granted/revoked.
This can be configured automatically using Knocker, or during Agent installation.
#!/bin/bash
IPSET_CONFIG="/opt/knocknoc-agent/etc/ipset.list"
# Read IPSET names from config
if [[ ! -f "$IPSET_CONFIG" ]]; then
echo "Error: IPSET configuration file not found at $IPSET_CONFIG."
exit 1
fi
IPSET_NAMES=$(grep -v '^#' "$IPSET_CONFIG" | grep -v '^\s*$')
for IPSET_NAME in $IPSET_NAMES; do
# Flush and create the IPv4 ipset
ipset -exist flush "$IPSET_NAME" || true
ipset -exist create "$IPSET_NAME" hash:ip
# Flush and create the IPv6 ipset
IPSET_NAME_V6="${IPSET_NAME}_v6"
ipset -exist flush "$IPSET_NAME_V6" || true
ipset -exist create "$IPSET_NAME_V6" hash:ip family inet6
doneSee more on IPset at the Netfilter project: https://ipset.netfilter.org/