VPN and Ransomware
Use Case: EliminatingRemoving SSHVPN AttackRansomware SurfaceRisk infrom aStolen Distributed EnvironmentCredentials
A largemid-size distributedbusiness enterpriserelied neededon Internet-exposed VPN appliances to eliminateprovide extranet access for staff, contractors, and business partners. Due to legacy constraints, some external users still used single-factor credentials.
After stolen credentials led to a ransomware incident, the attacksecurity surfaceteam ofacted itsfast—deploying Internet-facingKnocKnoc SSHto serversprotect -the withoutVPN addingedge latency,by changingorchestrating itsan networkexisting architecture,in-line or compromising on security. firewall.
The goal: tieeliminate network-level SSHInternet exposure and access to their identity provider, while keepingof the experienceVPN seamless.
Knocknocchanging wasnetwork deployedarchitecture usingor itsrequiring on-hostclient Linuxsoftware—critical firewall orchestration. Within days, all SSH services were rendered invisible until users authenticated, effectively removingfor the pre-authdiverse, attackdistributed surface.user base.
The result: zerono addedexposed hops,VPN, zerono user installation required, no routing changes, and a drasticallydramatically reduced riskattack profile.surface.
Technical how:
SSHIn canthis beexample, protectedan byexisting Knocknocin-line inFirewall aappliance numberwas oforchestrated ways:
Local Linux firewall orchestration onprotect thehostVPN(eg:andusingIPSets)In-line firewall/control device orchestration (Fortigate, JunOS, Palo, AWS, etc), via an adjacent Knocknoc Agent deploymentHAproxy can sit in front ofexpose theSSHservicesservice using the TCP feature
An on-host firewall orchestration approach is great for bastion hosts - or remove all SSH exposure from your external or internal environments.
This also allows Knocknocjust-in-time to effectively add SSO (and MFA) atop SSH, working together to add heightened security for bastion hosts, fast.
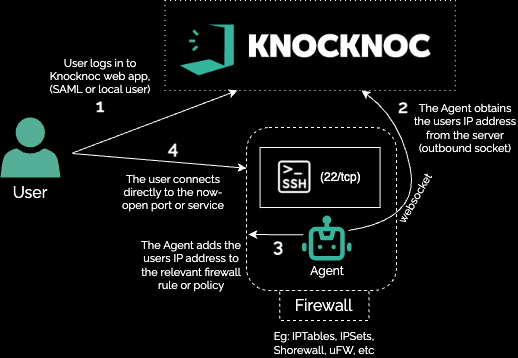
Shown below, the user first logs in to Knocknoc (auth tied to their IdP), the Knocknoc orchestration-agent then receives instruction to open the firewall to port 22/tcp from the users IP addressauthenticated and theauthorized user then connects. No proxy/broker, no additional routing nor client installation is required, simple but very effective firewall orchestration.
This essentially removes attack surface of your SSH hosts until users centrally log in.