Introduction
Welcome to the Knocknoc Admin Guide. This covers installation, administration, tuning and troubleshooting.
Your users might be more interested in the super-simple simple User Guide.
Setting up Knocknoc for the first time can appear easy, but it is important to understand how it fits into your whole security architecture. Knocknoc is an important component in reducing your attack surface, and allows you fine grained control over what resources each of your users can access. Users are generally expected to authenticate to those resources as well, in most cases, so please consider Knocknoc as part of a defence in depth strategy. In some cases, like video feeds, or SIP connections, extra authentication isn't workable, so you need to decide as part of your security strategy how to manage the risks.
Please have a read through the following sections, or jump straight the topic that interests you:
Getting Started
Access Control
Installing Knocknoc Server
Installing Knocknoc Agent
Configuring Backends
Authentication
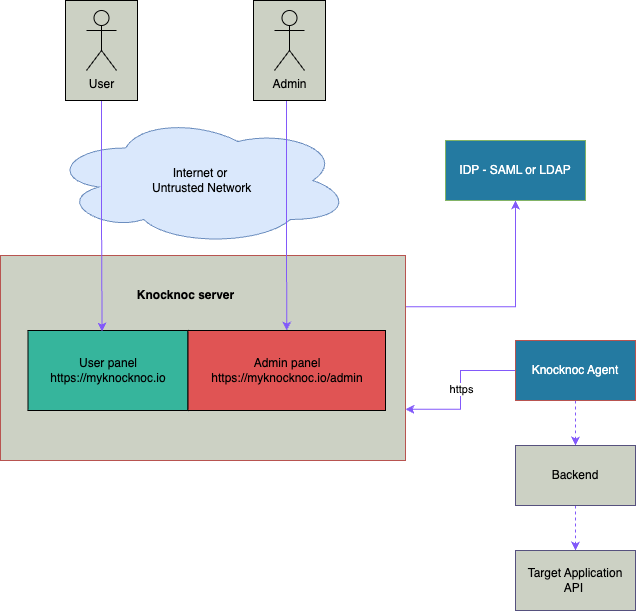
The architecture of a typical Knocknoc environment is often as follows: