High security subnets and JIT network access
Use Case: RemovingDynamic VPNJust-in-Time RansomwareIP RiskRestrictions fromfor StolenHigh-Security CredentialsSubnet
A mid-sizecritical businessinfrastructure reliedenvironment on Internet-exposed VPN appliancesneeded to provide extranetrestrict access forto staff,specific contractors,high-security andinternal business partners. Duenetworks to legacytrusted constraints,IP someaddresses externaldynamically, usersallowing stillaccess usedonly single-factorfor credentials.
Afterperiods. stolenThis credentialsapproach ledwould toensure athat ransomwaresystems incident,remained theinaccessible securitywhen teamoperational actedstaff fast—deployingwere KnocKnocnot toat protecttheir theterminals VPNor edgedid bynot orchestratingrequire aninteractive existing in-line firewall.access.
The goal: eliminateUsers Internetwishing exposureto access the high-security internal networks would log in to Knocknoc, granting network access and direct control-system protocol access to the target network for a period of the60 VPN without changing network architecture or requiring client software—critical for the diverse, distributed user base.minutes.
The result: noThe exposedhigh-security VPN,network nowas userprotected installation required, no routing changes, andby a dramaticallydefault-deny reducedfirewall attackpolicy, surface.with access granted only when an operator required interactive access. During that time, the terminal's IP address was dynamically allowed short-lived access.
A beneficial byproduct of the process was that all VPN user access permissions were reviewed, with many uplifted and migrated to their Entra External list allowing MFA to be enforced.
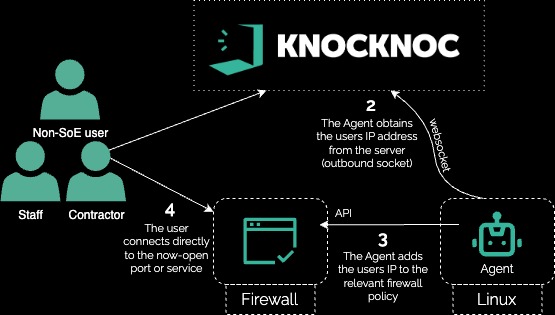
Technical how:
In this example, an existing in-line Firewall appliance was orchestrated to protect the VPN and expose the services just-in-time to authenticated and authorized users.