HAproxy
HAproxy is fantastic reverse proxy with a massive amount of features. Knocknoc has supported HAproxy for years, and integrates with it natively. The vast amount of options for HAproxy can make it confusing at first, however we can walk through the bare essentials to be able to use Knocknoc, and you can extend it from there.
If you wanted to protect an arbitrary web application, for example a legacy PHP app, or Atlassian Confluence, we would recommend deploying HAproxy to sit in front of the application, and use Knocknoc to control access. This will often be an easier deployment path, and is a cost effective security measure for many reasons.
HAproxy Admin socket
Knocknoc supports HAproxy's admin socket directly, so you can just configure the socket path, adjust the permissions and away you go.
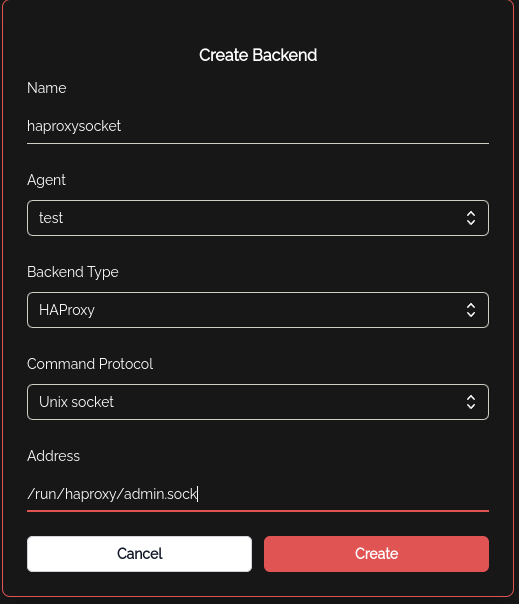
You can see from this screenshot, when you create a new backend, you can select HAproxy as the socket type, and then add the path. This implies your knocknoc-agent 'test' can read and write directly to the socket. One way to allow this is to add the knocknoc-agent user to the haproxy group:
adduser knocknoc-agent haproxyWorks on debian, or equivalent.
Haproxy TCP Socket
The HAproxy backend also supports a TCP socket, in which case it still expects to talk to the unix socket, but it can do so via a TCP redirect. This is most easily accomplished with the spiped utility.
knocknoc-agent ships with a script make-spiped-tunnel.sh which can walk you through making an spiped encrypted tunnel between your knocknoc-agent machine and a remote haproxy. It is often easier to deploy knocknoc-agent directly to a machine, but in case this isn't possible, you can use an spiped tunnel for this purpose.
Haproxy Configuration
Haproxy configuration is vast topic, however here is a minimal config for the seasoned admin to get started quickly:
frontend https_frontend
mode http
bind *:443 ssl crt /etc/ssl/private/ alpn h2,http/1.1
acl is_confluence hdr(host) confluence.mycompany.com
acl is_http hdr(X-Forwarded-Proto) http
acl knoc_confluence src -u 500
redirect scheme https if is_http
use_backend confluence_backend if is_confluence knoc_confluence
backend confluence_backend
mode http
server confluence_server internal_confluence_ip:443 check ssl verify noneThis config snippet sets up an HAproxy fronted on port 443, with certs served from the directory /etc/ssl/private and enabled HTTP2.
Then it sets up some ACLs for the hostname and Knocknoc to update (ACL ID 500).
Then the use_backend directive only allows connections to the backends if the hostname matches confluence.mycompany.com AND the list of source IPs in ACL 500.
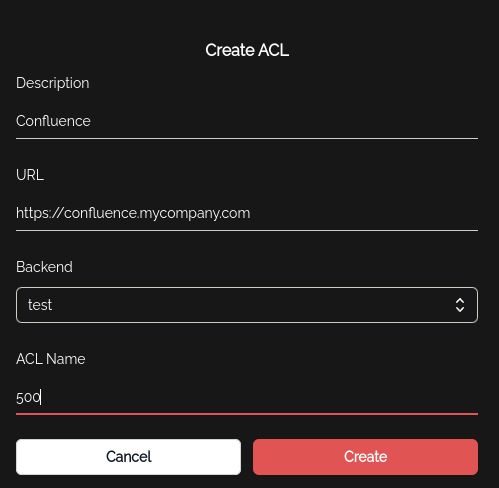
Knocknoc will then be configured using the ACL setting pane to have ACL 500 map to this backend on this agent:
Then this ACL needs to be added to a Group, and any user in that group will have their Source IP added to ACL 500 when they authenticate OK to Knocknoc!
Error Responses
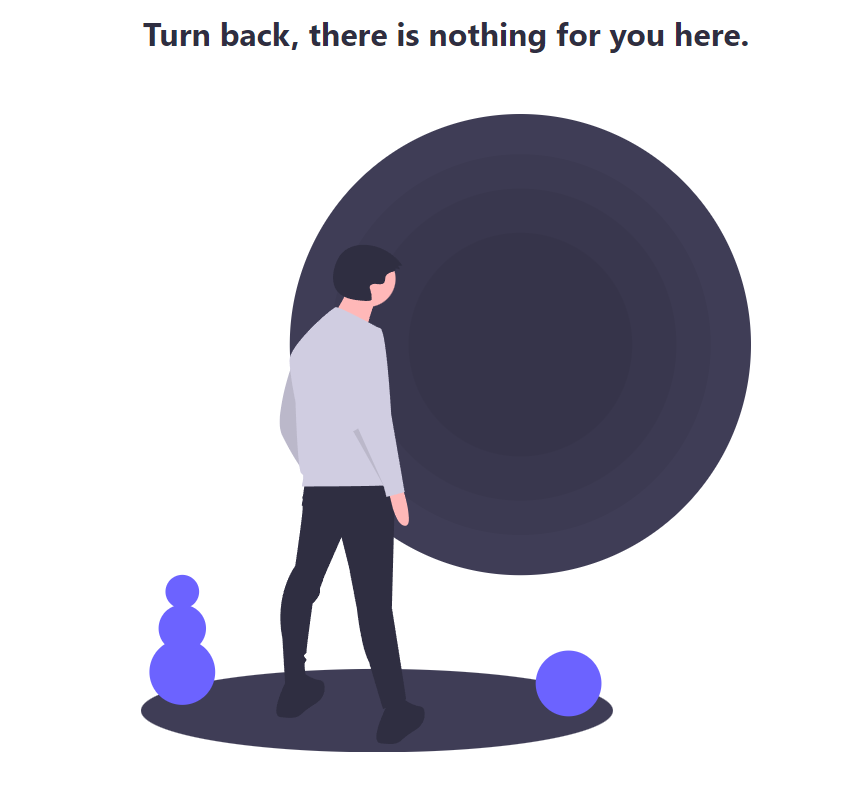
HAproxy can easily send custom 403 or 503 responses to users who aren't allowed to access the backend resource. For example:
This is configured as the default_backend error response in the haproxy config, so if the http request doesn't match the right source IP or hostname, the above is show to the browser. An admin can customise this to display whatever you like, but keep in mind its an HTTP response, not an HTML page, so there are limitations. You could of course link people to your Knocknoc instance in the error message, depending on your users and risk profile.