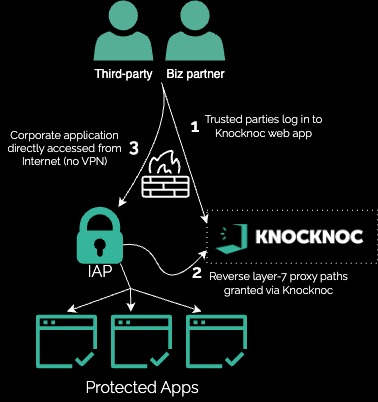
Financial services data partner, secure web upload
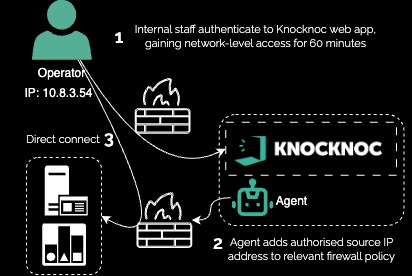
Use Case: DynamicTrusted Just-in-Timepartners IP Restrictions for High-Security Subnet
A critical infrastructure environment needed to restrictsecure access to specificweb high-securityapplication
internal
A networksfinancial services provider relied on periodic uploads through an Internet-exposed web application. Although the application was actively maintained, it posed substantial value and risk to trustedthe IPorganization addressesdue dynamically,to allowingthe accesshighly onlyconfidential, proprietary investment information it contained.
The goal: Eliminate the attack surface of the highly confidential, internally-built web application used for short-livedcollecting periods.proprietary Thisinvestment approachinformation. Trusted third parties and business partners would ensurebe that systems remained inaccessible when operational staff were not at their terminals or did not require interactive access.
The goal: Users wishingrequired to access the high-security internal networks would log in to Knocknoc,Knocknoc grantingbefore networkaccessing accessthe web application, enhancing edge security and directmitigating control-system protocol accessrisks to the targetapplication.
The result: The web application's exposure to the public Internet was eliminated without significantly disrupting the access flow for aexternal periodbusiness ofpartners 60and minutes.
Theproviders. result:Pre-auth Theweb high-securityapplication networkpaths, wasAPI protectedroutes, byand other potential attack vectors were removed. Both Knocknoc and the web application were integrated with the same Identity Provider (IdP), delivering a default-denyseamless firewalluser policy,experience withwithout accessrequiring grantedany onlyend-user when an operator required interactive access. During that time, the terminal's IP address was dynamically allowed short-lived access.installation.
Technical how:
In this example, ana existingreverse in-lineproxy Firewall(HAProxy appliancein this case) was orchestrated toby openKnocknoc, opening up access justto inlayer-7/HTTP timefiltered andpaths removeto accesstrusted onIP logoutaddresses oronly timeout.after they successfully authenticated to Knocknoc.